
“Cybercrimes are becoming mainstream,” NSK Inc. IT Consultant Philip Abraham said, “the internet is full of predators.”
With cybercrime becoming more prevalent in our society, computer safety is something that must become an unfortunate priority. Thankfully, the experts here at NSK Inc. are more than prepared when it comes to this stressful aspect of the IT world. So instead of searching the internet for common sense fixes and confusing techniques, the NSK team has gotten together to create a list of precautions and steps to ensure your devices stay safe.
1. Keep a Backup
“One of the safest ways to protect your data is to have an external backup of it,” Sr. IT Consultant and Account Management Supervisor Jason Masterson said, “Antivirus is great, but it is not 100 percent, and if something gets through, having a backup can be a life saver.”
The best way to go about this, while it might seem tedious, is to save your important information in more than one place.Saving the data to your computer is always step one, but where else should you save it? NSK Inc. actually offers their own backup program called “Pavis.” The benefit of Pavis is that is provides the large scale availability of a public cloud, with the security of a private one. It is a data recovery program as well as a backup system that allows you to feel secure that even in the event of physical system failure, that your information is safe and secure.

“Storage is a large problem for our clients. In the past, Cloud Computing has been expensive to scale. Now, Pavis Cloud Solutions allow our customers to continue to store and share data as they always have while implementing a secure, cost effective, scalable solution,” President of NSK Inc., Timothy J Lasonde, said in an article by hostreview.com.
The main advantage of Pavis is that is can be tailored to each client’s needs and will continuously backup the user’s data every 15 minutes, 24 hours a day. Not only that, but you get the security of the program being fully administrated and monitored by NSK technicians, so you know you’re getting high quality protection and service.
2. Use Security Programs
One of the easiest things you can do to keep your computer safe is to download programs that help keep track of security for you. While in the past anti-virus and adware/spyware programs were sold individually, most applications now will cover both aspects.
“Use a good Anti-virus, most paid versions are better than the free ones for the average user, and stay away from McAfee,” Sr. IT Consultant and Project Manager Brian Steen said.
It is important to note however that having more anti-virus programs doesn’t make your computer that much safer. In fact, having more than one anti-virus program running at a time can actually hinder the program from functioning properly. Both Windows and OS X come with built-in security software, though third-party programs are also available.
Sophos is a well trusted brand that offers both free and paid versions of their security programs. For the average user there is Sophos Home, which is entirely free and works on both Windows and Mac OS. It is designed to protect up to 10 devices for free as long as it is for private, non-commercial use. For larger scale servers, Sophos offers several different packages at various prices.
On top of having a quality anti-virus program, there are other steps you can take to ensure not only your business, but personal information is safe as well. “Identity Finder” is a program that is designed to locate and secure personal and private information that you enter on your computer. It can encrypt, shred, or even redact information once it’s found, will organize the files where this information is found, and overall will ensure that a hacker or laptop thief won’t be able to steal anything important. According to SC Magazine, which gave the program a 5 star rating, the only downside is the price tag. It costs “$17,500 for 100 seats” according to SC. Designed to be used for medium to large firms, if you can afford the cost, this is the highest recommended product.
3. Change Your Passwords
“Keep your password complex and secure. Use symbols and do not include words or numbers that are personal to you that maybe easily be guessed,” is Masterson’s biggest tip when it comes to password security.
While it may seem like common sense, a lack in password security is one of the easiest ways for hackers to get what they want.

According to Skyhigh Networks, “10.3 % of [computer] users” rely on the same 20, insecure passwords. 4.1 % of that group used the password “123456” and 1.3 % used “password” as their password in 2015.
When creating your password for any new app or website, Windows recommends that you remember these tips:
- Your password should be at least 8 characters long
- It should NOT contain your user name, real name, or company name
- Don’t use a complete word
- Make sure this password is different from previous or other current passwords
Related to the topic of changing passwords is the idea of using the Principle of Least Privilege or PoLP. This idea basically states that unless you have to perform a specific task, you should never log in as an administrator or upper level login. By signing in with an account that has lower clearance, it leaves your computer less vulnerable to attack.
Never revealing your passwords or passphrases is also important, which brings us to our next tip.
4. Know Your Vendor
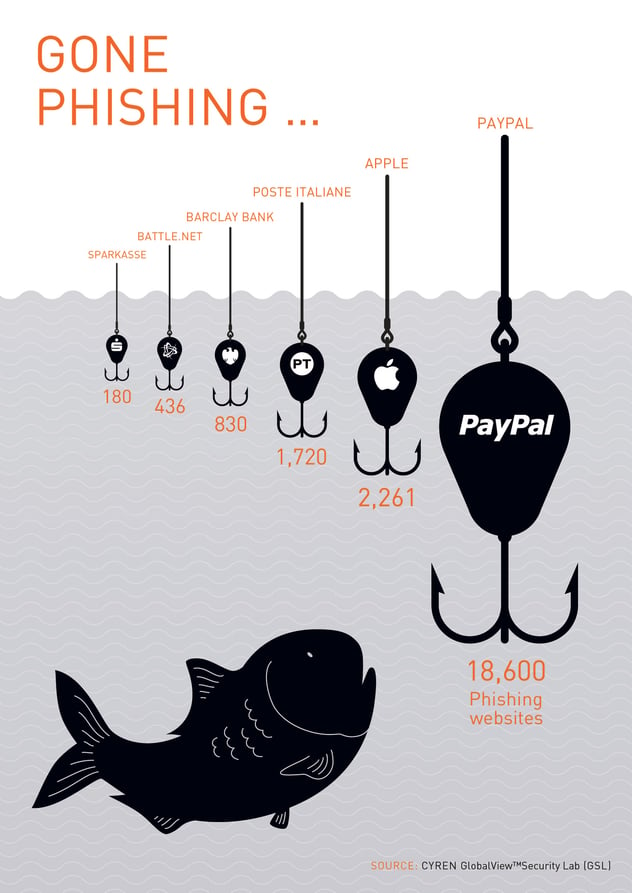
Social Engineering is defined as “a non-technical method of intrusion hackers use that relies heavily on human interaction and often involves tricking people into breaking normal security procedures,” (Tech Target) and right now it is on the rise.
These attacks can come in several forms and are becoming all the more sophisticated as time goes on. Spanning from an email that appears to be from a credit source to phone calls, malicious links, popup ads saying you need to clean your computer, etc.
“Never give your personal passwords or billing information out over email or to people calling. Few, if any companies will call or email asking for their details," Masterson said, "If someone does call asking for this information, hang up and call the company they claim to be from. But Microsoft, or other vendors will never call asking for money or billing information or remote access to your computer."
When all else fails, remember to always ask your professional IT consultants any questions you might have.

