The U.S. Government has been regulating Information Technology within the private sector for years. There are compliance laws such as Massachusetts’ 201 CMR 17 and the HIPPA Act of 1996 that outline how companies and organizations are supposed to store personal information of their employees and their customers/clients. However, our own government recently failed a security audit for failing to keep their systems updated in a timely manner.
Uncle Sam sure can dish it out, but apparently, he can’t take it.
The Findings
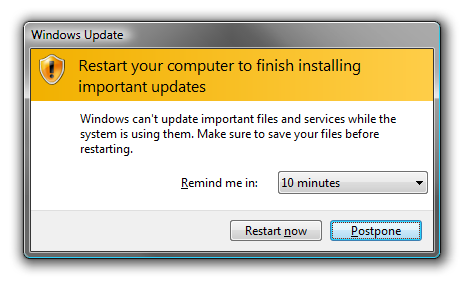
A report by government auditors found that systems at the U.S. Computer Emergency Readiness Team (aka CERT) which is part of the National Cyber Security Division of the Department of Homeland Security “were not maintained with updates and security patches in a timely fashion and as a result were riddled with vulnerabilities.”
An anonymous former Homeland Security official claims that the problems happen everywhere. “Ask any IT department in any large enterprise … There is no network that is 100% patched. Eighty-five percent is a good number.”
Other Views
I spoke with NSK’s resident IT Security Expert, Ben Howard, who responded with this:
Patch management works and works well, but only in a well administered and well designed network. If you lack proper asset management, configuration management, and administration, the patch management will definitely fail.
However, when you have processes in place to design, configure, and implement network resources in a standardized and secure fashion, patch management can become almost completely automated with near 100% patching in a very short period of time.
There are always a few [systems] that don’t patch for various reasons (PC may be turned off, etc), and these are tracked down and manually patched. It is true that no network will be 100% secure, but 100% patched is not a pipe-dream. It is a reality for a well run IT department.
Clearly the CERT officials were trying to displace blame. The fact that the National Cyber Security Division part of the Department of Homeland Security failing a Security Audit is incredibly confounding.
The Bottom Line
If something is wrong, fix it -don’t blame someone else. Also, if you haven’t done so already, have a Security Audit performed at your organization. You’ll be glad you did.
