A SOC 3 report is designed to meet the needs of organizations that want assurance for their Clients on the controls the organization uses in relation to security, availability, processing integrity, confidentiality, or privacy. The Report is an easily publicly distributed report and is designed to attest to the Organization’s successful completion of a SOC 2.
SOC 2 Reports are for your clients that need to understand the internal controls at your organization as they relate to security, availability, processing integrity, confidentiality and privacy. These reports can play a very important role in the oversight of your organization’s vendor management programs, internal corporate governance and risk management processes and help to comply with regulatory oversight. The report only includes information relevant to public parties. These reports are prepared using the AICPA/ CPA Canada (formerly Canadian Institute of Chartered Accountants) Trust Services Principles and Criteria for Security, Availability, Processing Integrity, Confidentiality, and Privacy.
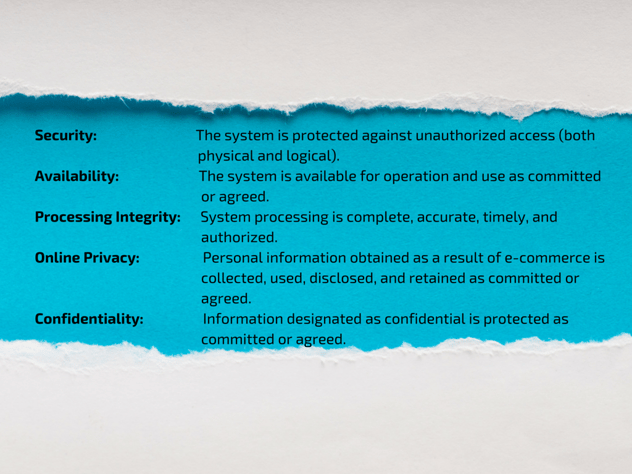
The SOC 3 Report, is just like SOC 2, in that it is based upon the Trust Service Principles and performed under AT101, the difference being that a SOC 3 Report can be freely distributed (general use) and only reports on if the entity has achieved the Trust Services Criteria (no description of tests and results or opinion on description of the systems). SOC 3 reports can be issued on one or multiple Trust Services principles (security, availability, processing integrity, confidentiality and privacy) and allow the organization to place a seal on their website upon successful completion.
The Trust Service Principles were designed with a focus on e-commerce systems due to the amount of private/confidential/financial information that flows across the internet daily. When a transaction is processed for a customer/client , or the customer/client builds a business on your service (SaaS providers), or submits private information, they want to know best practices are being followed by the organization to guard against security leaks, lost sales, and damaged data.

