So you have a Nigerian prince in your emails who seems nice enough. He’s never been anything but polite, and from the looks of it, he has had a rough time lately. As it turns out, being a prince is not as lucrative as it sounds. He just needs $12,000 from you to make it all better.
You know how this story ends. You laugh it off because you know it’s a scam – you don’t know this guy, why would you ever give him money?
But what happens when someone you do know emails you out of the blue, needing some cash? Or if a coworker asks for access to a file? Or if someone you’re pretty sure you know sends you a link that you just have to click?
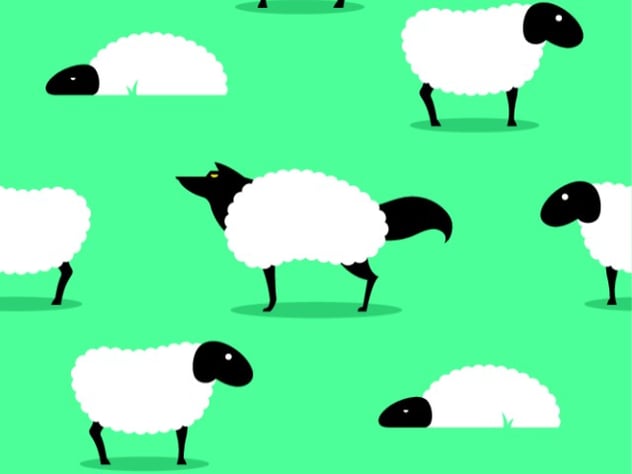
This is social engineering, and it is a clever old trick revamping itself for the modern era.
All of the above situations qualify for social engineering: they consist of scenarios where you are socially manipulated into giving up information.
Sometimes examples of this are not as obvious as the Nigerian prince.
As Webroot writes in a blog post about social engineering, the biggest threat to your company’s security might not be a hole in the firewall but an overly trusting employee. Someone who appears to be a client or coworker may contact them asking for access to information, and if the employee is not paying close attention they may be sending confidential files to an attacker.
“If you trust the person at the gate who says he is the pizza delivery guy and you let him in without first checking to see if he is legitimate you are completely exposed to whatever risk he represents,” says Webroot’s Linda Criddle.
Common social engineering attacks
- Email from a friend or coworker requesting a password: Attackers will use a victim’s contact list to bait even more people into giving up their information. If you receive an email from a friend that asks you for your password to ANYTHING, do not give it to them, unless you have had a conversation regarding the information.
- Message to update your Flash player: If you are prompted to update your Adobe Flash program in order to watch a video online, you may want to be especially cautious and check to see if that is necessary, as you might be falling into a trap to install malware onto your device.
- Impersonators: You may receive a call or email from someone pretending to represent the IRS or an IT service person who wants you to wire in money or risk serious consequences. If their story seems too good, remember this: the IRS doesn’t make house calls, and Microsoft has no idea who you are, or what kind of computer you use.
Always practice common sense when you get an unprompted request for information. If a site says that it’s free but still needs your credit card information, chances are it’s not actually free and you’re playing right into an attacker’s hands.
Sources
Image courtesy of Kaspersky Lab blog: https://blog.kaspersky.com/social-engineering-hacking-the-human-os/3386/
